Page Contents
The saying “you have to take the good with the bad” applies perfectly to social media’s relationship with businesses that rely on it. Utilizing social media channels to drive more traffic to your website or increase a conversion rate can give your enterprise a significant boost for an affordable price.
Simultaneously, social media poses a severe risk when used carelessly. For example, an irresponsible tweet with a not-so-good joke cost Electronic Arts a great deal of backlash.
Another illustrative example is ex-presidents Donald Trump’s Twitter account hack. Trump’s failure to adhere to safe password management almost caused a political avalanche. Imagine the damage to the administration if that was a pre-planned coordinated attack with ill intent.
Using Mark Zuckerberg’s words, social networks can truly move fast and break things. Next year marks the twentieth Facebook birthday, so let’s take a look at how social media shaped our contemporary business landscape.
What Happened During Twenty Years of Social Media?
To be honest with facts, the title of the first social network is attributed to SixDegrees social network, created in 1996 and launched the following year. It offered similar features to Facebook, like profiles, a friend list, etc. It was several years ahead of its time because there simply weren’t that many people connected to the Internet.
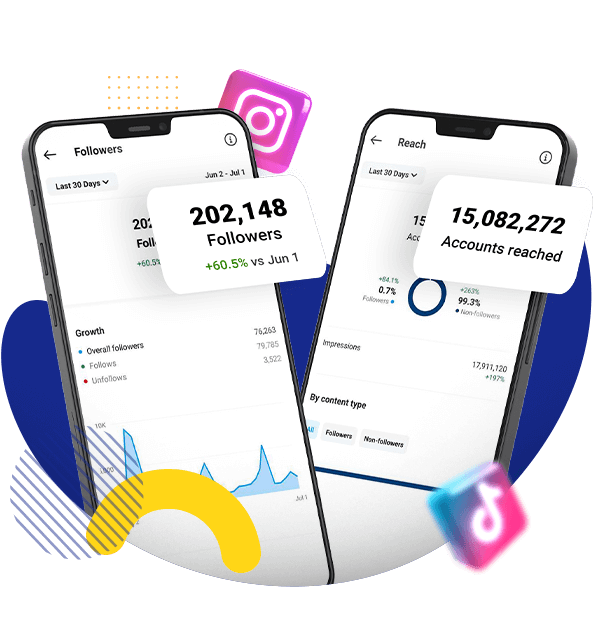
Ironically, 1996 marks the year when things really kicked off, doubling Internet size compared to the previous year. Ten years later, it’s more than ten times its size, and now more than half of the world’s population spends time online. Currently, nearly three billion people have a Facebook account, two billion use Instagram, and one billion use TikTok. Twitter, and Reddit are a bit short of half a billion.
This rapid migration to online spaces opened endless business opportunities. Unsurprisingly, numerous BigTech companies are among the most profitable worldwide, with Amazon outperforming Volkswagen by two hundred billion in revenue, even though it was founded more than half a century later. It is forecast for e-commerce sales to reach $6.3 trillion and online purchases to make 20% of the whole global sales in 2023.
Social networks played an extraordinarily big role in developing online markets. As Forbes put it, “to question the power of social media in society is to question the importance of sunlight on earth.” Right now, brands can expect to reach 10% more people than their follower count by posting on Facebook, and more than two-thirds of marketing professionals use social media to develop long-lasting relationships with loyal brand fans.
Social Media and Cybercrime
Cybercriminals were quick to shift attention to online markets. Moreover, the uncontrolled expansion of the Virtual produced hundreds of vulnerabilities, leaving cybersecurity several years behind. Once again, social media played a significant role in this.
According to Comparitech’s data, in 2020, there were 500 social media groups with 220,000 members dedicated to fraud, 60% exploiting the Facebook platform. Moreover, cybercriminals use the same social networks they hack to promote their services, sell hacking software, and recruit new members.
Unfortunately, social media is very susceptible to shady practices. Facebook has been exploited to undermine the 2016 U.S. presidential elections, Twitter – to spread misinformation, and WhatsApp – for human trafficking, so the list goes from bad to worse.
Furthermore, it’s much harder to identify a bad actor over the Internet than during facetime. It is particularly important for businesses with strong online presence because cybercriminals will do their best to trick employees into downloading an infected email attachment, clicking on a fraudulent backlink, or sharing their passwords.
To summarize, social media is highly ambivalent. It is one of the most powerful marketing tools that can capture the essence of your brand and communicate it to billions of consumers if you do it right. On the other hand, using social media as a primary business image-building tool requires careful consideration because social media cybercrime spreads like wildfire.
It’s best to come prepared to mitigate possible online risks. The second half of the article will outline the specific online threats you should be aware of and how to avoid them.
Social Media Risks for Businesses
The weakest link in the majority of cybersecurity systems is human error. That means effective business security must consider employee training as much as cybersecurity software. Let’s start with the most common threats.
Data Mining
Social media was created to share information. During the first years of Facebook, users shared excessive amounts of personally identifiable data without thinking twice. Nearly two decades later, 72% of U.S. citizens distrust Facebook, Instagram, and TikTok in handling their personal information.
A huge blow to Facebook’s reputation was the Cambridge Analytica scandal when it illegally harvested 87 million Facebook profiles and used them for political advertising for Ted Cruz and Donald Trump campaigns. The situation worsened when Facebook started regularly leaking user data, unable to secure its platform.
Sooner or later, leaked data appears on online black markets available to the highest bidder. Cybercriminals often receive such information:
- Name and surname;
- Phone number;
- Physical and email addresses;
- Social security numbers;
- Username and password hashes;
- Financial data (credit card number, tax information, credit score, etc.).
When in the wrong hands, such data can become a powerful weapon. Hackers can use it to take fake loans, steal online business accounts, impersonate chief executives to issue false orders, or use it for other upcoming frauds.
The lesson here is rather simple, which Netizens learned the hard way: do not overshare on social media. Even if you have robust privacy settings, a person in your friend list could expose your information if they get hacked. Moreover, social networks aren’t exactly known for being reliable security-wise. Trusting them with your personal data is like investing in a Ponzi scheme: once it gets big, it comes crashing down.
However, that doesn’t mean you must isolate yourself without sharing anything online. Trusting your data with companies that put effort into securing it is best. For example, you can use secure Cloud storage to keep your pictures and videos in an encrypted Cloud. You can access this information anytime, share it over end-to-end encrypted chats, like Telegram, and delete it permanently afterward to prevent leaking sensitive information.
Phishing and Social Engineering
Data extracted from social networks is often fueled by Social Engineering and Phishing attacks. Even though they are not synonymous, the differences between them gradually diminish.
To put it short, Social Engineering relies more on psychological manipulation and Phishing – technology. However, phishing attacks use psychological pressure nowadays, and Social Engineering utilizes various hacking software. In this article, we will use them interchangeably.
Phishing often utilizes email services to spread malware and other online dangers. Remember the infamous Nigerian Prince scam? As unconvincing as those emails were, many people still fell for them because they never imagined such dangers existed online. The situation significantly worsened after people started oversharing online.
For example, a very effective and highly sophisticated method is Website Cloning spread via Phishing. Hackers construct from scratch a mirror website – frequently of a trusted bank – and lure unsuspecting Internet users via email. Two decades ago, they had limited information to work with, providing a genuine name, surname, and telephone number at best. Right now, such letters include personal information, banking details, SSN, and convincing senders’ information because bank employees also overshared online.
The victim is incentivized to go to the bank’s website link inside an email. Because the website is a perfect copy of the original and sometimes even has a security certificate, people hastily input their login details, providing cybercriminals access to their bank accounts.
Phishing is frequently used to target businesses to extract valuable information, such as software credentials or R&D data. A common scenario is sending a letter from HR with an invitation to a business party with an attached program. But instead of getting refreshments, you get a virus.
Defending against Phishing attacks is a multi-layered process. Firstly, employee cybersecurity awareness training is mandatory to identify incoming threats. Such programs include:
- Phishing identification;
- Social Engineering tactics;
- Business network security;
- Home network security (for WHF workers);
- Password management;
- Healthy browsing habits.
Furthermore, you can simulate a few cyber incidents to verify their awareness. If some of your employees still can’t identify common online threats, you can repeat the training because cybersecurity takes time to get used to.
Credential Stuffing Attacks
Businesses are particularly susceptible to Credential Stuffing attacks because they can be used to break into a company’s network.
This time, hackers rely on numerous online password leaks. The leaked username-password combinations from Marriott, Equifax, Yahoo, and others are sorted into huge lists and sold on black markets. Cybercriminals that buy such data use automation software to target thousands of different online service accounts, hoping someone will use the same credentials more than once.
Password management is not unlike fast food: you know it’s not a good idea for that fifth cheeseburger, but it’s fast and easy! Jokes aside, Internet users will use fast, easy, and comfortable passwords if it gets them easier access to online accounts. Furthermore, if your employees switch between multiple accounts, typing a long and complex password will significantly slow them down.
Letting them reuse easy-to-guess passwords for business account protection is a recipe for disaster. Luckily, aside from educating your employees on various cyberattacks and tools, such as VPN service, there are two straightforward ways to get outstanding Credential Stuffing protection.
Firstly, you should subscribe to a business password manager and train your employees on using one. A business password manager stores all passwords in an encrypted vault, locked by a single master password. Instead of remembering dozens of unique combinations (or writing them down in a passwords.txt file on a desktop), they only have to remember a single master password.
What’s more, the vault is protected by advanced encryption algorithms that would take a decade to break with current technology. A systems administrator can modify and monitor vault user access points, knowing who and when accessed the vault at all times.
A second highly-efficient method is Multi-factor-authentication (MFA). This cybersecurity feature allows choosing secondary identity verification methods, such as:
- An additional security question;
- Email code verification;
- SMS code verification;
- USB security tokens;
- Biometric verification;
- Authentication apps.
The secondary step prevents unauthorized access even if the hacker manages to crack the username-password combination. Stuffing a reused password is one thing, but how will they get biometric data or a unique USB security token?
MFA methods are one of the safest ways to protect valuable online accounts, but they do not render password managers useless. In fact, it’s best to combine the two. Use a password manager to store unique, complex passwords in an encrypted vault. And use multi-factor authentication to protect vault access.
Managing Online Reputation
Social media can ruin your business without any hacking involved. For example, four years after the devastating 2013 Boston Marathon bombing, Adidas somehow thought to send a “Congrats, you survived the Boston Marathon” mass email. Needless to say, the participants did not take that lightly, and Adidas had to apologize.
It looks like only Elon Musk can get away with spontaneous tweeting, but it’s best not to push the limits. Remember, whatever you post online stays there. It takes one unfortunate social media mismanagement to stain your brand for decades, and Internet users rarely forget significant failures.
When using social media for your business image, it’s always best to withdraw from personal feelings and culturally sensitive topics. Let your brand speak for itself and product quality back it up, and you will have a dedicated online community before long.
Conclusions
As with every new groundbreaking technology, a little chaos is involved in the beginning. It takes time and experience to master social media, and we hope this article illustrates several online threats you should prepare for. However, if you use it safely and respectfully, you can expand your brand and communicate with potential consumers worldwide. Moreover, in the long-term social media will generate stable revenue and is one of the best conversion-driving channels.